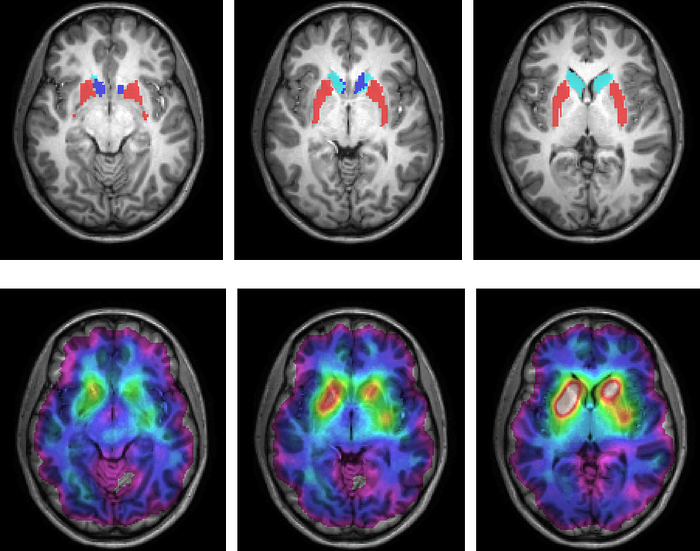
As a Neuroscientist, I Quit These 5 Morning Habits That Destroy Your Brain
Most people do #1 within 10 minutes of waking (and it sabotages your entire day)

AI-Driven Black Box Active Directory Penetration Testing
Fully Automated AD Discovery and Exploitation with Cursor AI and HexStrike-ai MCP. From IP to...

Master Web Fuzzing: A Cheat‑Sheet to Finding Hidden Paths
Hey there, back again with another post! 😄

Guardian: An AI-Powered Penetration Testing Automation Platform
Penetration testing has always involved trade-offs. You either go manual, which is deep but slow...
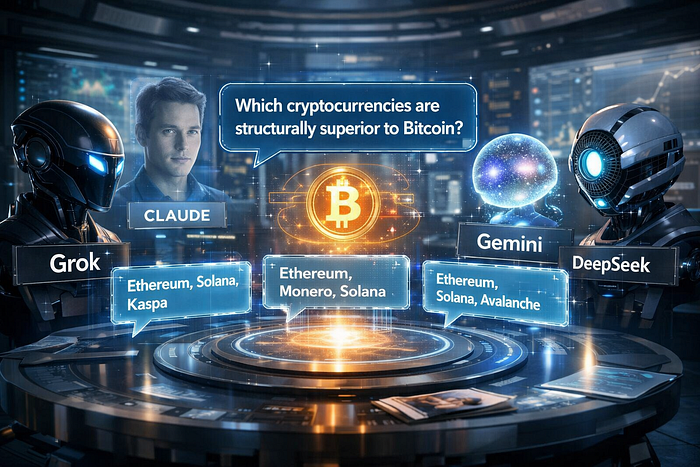
I Asked Four AIs What Cryptocurrencies Are Better Than Bitcoin — And They All Agreed
Well Mostly Agreed — Together They Came Up With 5 Compelling Names
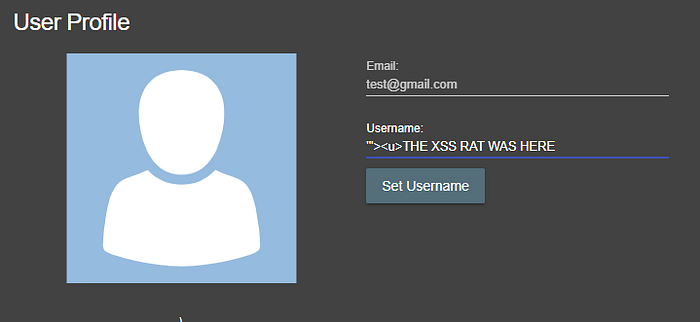
How i found my first 3 bugs in public program in bugcrowd
"بِسْمِ اللَّهِ، وَالْحَمْدُ لِلَّهِ، وَالصَّلَاةُ وَالسَّلَامُ عَلَى رَسُولِ اللَّهِ،...

HexStrike MCP Orchestration with Ollama: Ubuntu Host, Kali VM, SSH Bridging, and Performance…
How to wire Ubuntu (Ollama) to Kali (HexStrike) with MCP over SSH, what models actually behaved...

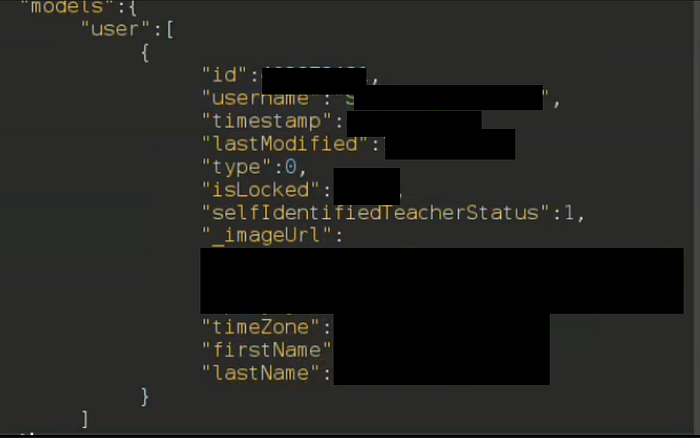
$1,000 Bounty: How I Discovered a Parameter Pollution Bug That Leaked Sensitive Data
A simple trick with duplicate parameters exposed hidden data on Example.com — here's how you...
Advanced Linux PrivEsc Toolkit: 15 Modern Tools Every Ethical Hacker Should Master
Ever landed a low-privilege shell on a Linux box and thought, "Now what?" You're not...

Stop Fuzzing Blindly: The Ultimate Guide to FFUF
Most hunters use 10% of this tool's power. Here is the advanced "Sudoaman Config"...
Prompt Injection Toolkit: 25 Payloads & Techniques for Mastering AI Pentesting
Ever tried breaking an AI chatbot with a 'please ignore all previous instructions' prompt,...
Agentic AI Red Teaming: The Hottest Cybersecurity Career of 2026 (Beginner-Friendly Guide)
How to Start a Career in Agentic AI Red Teaming (New 2026 Path)

AI-Driven Web Application Pentesting with HexStrike-AI
A Practical, End-to-End Guide to Modern Web Application Penetration Testing Using LLM-...

I Watched The '1,000 Men In One Day' Documentary
Once again, I have so many thoughts

5 Automation Scripts Every Linux User Should Know
In this article, you'll learn to create Bash scripts that solve common problems like...

Who Wins in the 2026 Cybersecurity Job Market?
Cybersecurity Is Splitting in Two: Here's Who Survives the AI Takeover
Why 'Full-Time Developer' Career Is Becoming Dead — And What's Replacing It
The Brutal Truth No One Wants to Admit

The Bug Bounty Automation Stack That Can Generate $10K+ (Open Source Tools Only)
Automation doesn't find bugs. Automated workflows combined with manual validation do. While...
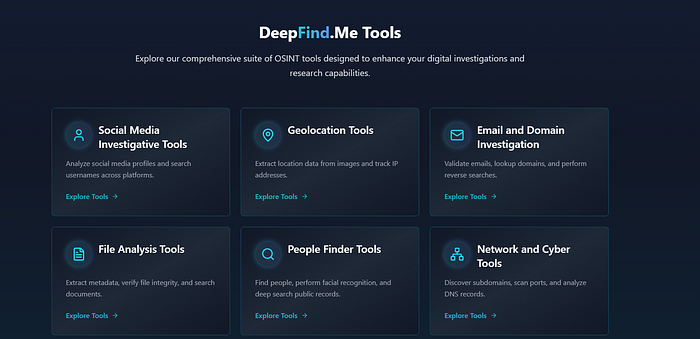
DeepFind.Me: Powerful Resource For OSINT Investigators
A Resource with combined OSINT tools
Top 10 Network Visibility Tools Every Pentester Needs in 2025: Level Up Your Recon
✨ Link for the full article in the first comment

Stop Using Free Wi-Fi: This Is How Attackers Steal Your Passwords in Seconds
At almost every café, airport, coworking space, and tech event, you'll find a network called...
The 7 Ollama Commands That Separate Hobbyists From Power Users
Running ollama run llama3 feels magical at first. You type a question, and a 7-billion parameter...

Kindle vs iPad Mini: I Ran a 15-Day Reading Experiment To Find The Better eReader
To find out the better eReader among the two, I ran an experiment. The numbers were close. The...

HexStrike AI: Install, Configure, and Run MCP with Gemini, OpenAI, Cursor, Llama
A practical, end-to-end guide to installing HexStrike AI, wiring it as an MCP server, and running...
I Stopped Using ChatGPT for 30 Days. What Happened to My Brain Was Terrifying.
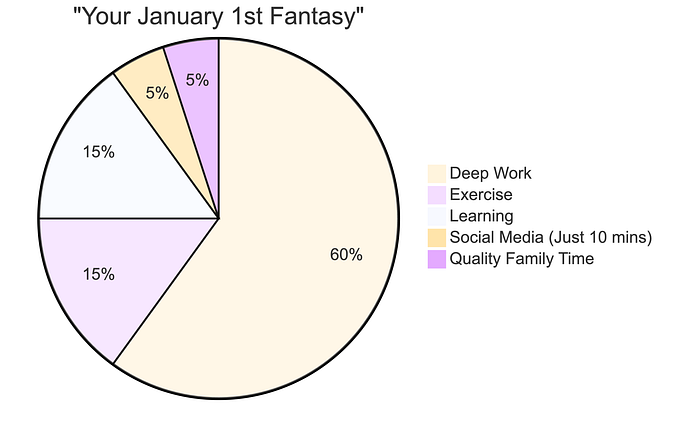
91% of you will abandon 2026 resolutions by January 10th. Here's how to be in the 9% who...

Threat Intelligence Stack for a Solo SOC Analyst (Free Only)
Most SOC analysts think threat intelligence means buying tools.

7 "Boring" Micro-SaaS Ideas Making $2k/Month (The Developer's Blueprint)
No AI hype. No complex algos. Just solving rich people's problems.
We Could Learn a Lot About Sex From the Dutch
My Dutch relative's views shocked me, but I immediately realized she was right

How I Passed the eJPT in 2 Months Without Losing My Mind (Or My Weekend)
I took two steady months, balanced it with my 8–5 job, my gym sessions after work, and my life...

Villager: The AI-Powered Penetration Testing Framework
How "Villager," a DeepSeek-driven framework from China's Cyberspike collective,...

From $0 to Your First Bug Bounty: A Beginner's 14-Day Roadmap (2026, No Paid Tools)
What Bug Bounty Really Looks Like for Beginners in 2026

🧰 My Bug Bounty Tool Stack (2026 Edition)

Bug Bounty Hunting: A Comprehensive Guide in English and french
· ~3 min read · February 12, 2026 (Updated: February 12, 2026) · Free: No🧰 My Bug Bounty Tool Stack (2026 Edition)
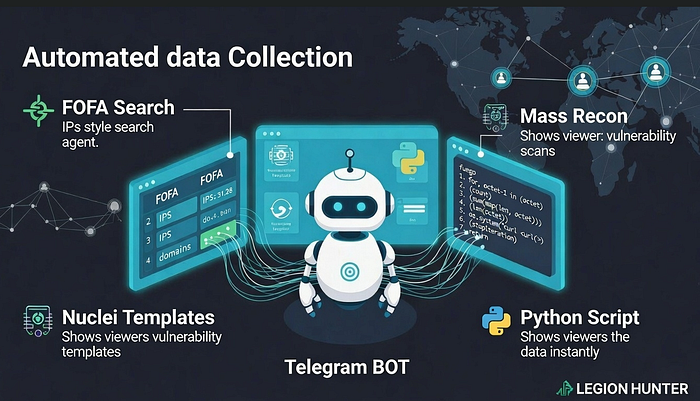
Telegram BOT OSINT using FOFA Dorking
Custom nuclei Template + python Script for OSINT and mass recon
The Open-Source Project That's Secretly Burning Companies
How a trusted library quietly breaks production while maintainers remain oblivious
Anthropic Just Released Claude Code Course (And I Earned My Certificate)
Anthropic just launched their Claude Code in Action course, and I've just passed — how about you?
The Complete Guide to AI-Driven Penetration Testing: Cursor, MCP, and the Modern PT Workflow
A comprehensive, step-by-step guide to running penetration tests the way that actually works —...

5 Obvious Ways Everyone Knows You're Using ChatGPT
This is what everyone says is a dead giveaway for spotting ChatGPT generated content
The Free, Open-Source Alternative to ElevenLabs Is Finally Here
The ultimate TTS suite: professional voice cloning, design & emotional control. Own it,...